This time it is not about just a single API exposing data. Dialog online login vulnerability was way more bigger. Someone else can login to another person’s account & change their data plans, activate / deactivate packages, check / change personal data and so on. So I decided not to write anything in detail related to the vulnerability until Dialog fix it.
First of all I should say same as Mobitel, it was not easy at all for me to escalate the issue to Dialog. It was like the security vulnerability was my fault. I noticed this vulnerability even before I found Mobitel API expose NIC number issue. So initially I tried contact them via Facebook fan page & Twitter. They replied they will inform relevent departments. And same day I informed this to one of my friend who is working at Dialog, but nothing happen for more than two weeks.
So then I contacted several Dialog security engineers, most of them didn’t even reply, but managed to send screen recording reproducing the vulnerability to Dialog security team. By the time I publish this blog post, it is already 4 days gone, but still the issue is there. And also no one from Dialog accepted that it is a vulnerability as of today.
This is not just an intern or junior developer accidently exposing data from an API. It was an architectural issue which I believe Dialog security team or some external party pen tested & signed off. Basically every time you login to Dialog online portal, there is a chance someone else can get your SSO token & log in to your account. Don’t need hacking tools, packet tracers or anything fancy. Just one curl command is more than enough. You don’t need to access any Dialog servers for this, SSO token of user logins publicly available.
Hopefully Dialog will fix this vulnerability within few more weeks. Or at least accept that it is a security loophole in their system.
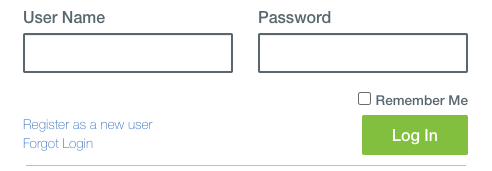
By the way, do you know what is the most useless User Name, Password login form in the world? Go to dialog.lk & click Login button.
Cheers,
DilumN

